The ability to meet the ongoing data security and privacy compliance requirements of the healthcare industry is key to ensuring the long-term success of digital health businesses.
All digital health organizations, regardless of their size, can expect to face a variety of stage-specific compliance challenges as they grow and scale. These may include:
- Building a compliant cloud infrastructure
- Managing secure deployments
- Passing enterprise audits
- Obtaining key industry certifications like SOC 2
- Maintaining multi-region support
Some organizations might opt for shortcuts, particularly those in earlier stages of business. But downstream complexities can lead to even bigger hurdles in the long run, especially when it comes time to engage with healthcare enterprise systems.
Healthcare enterprises like hospitals and insurance companies are legislatively mandated by the Health Insurance Portability and Accountability Act (HIPAA) to protect the privacy of their patients’ personal health information (PHI).
Digital health solution vendors need to prove their ability to uphold these obligations in order to earn the trust of healthcare service organizations prior to partnering or selling.
The Compliance Continuum
It can be helpful to think about compliance as different stages along a journey, with varying risk profiles and requirements along the way.
For simplicity we’ve grouped these requirements into three distinct phases, although in reality, it’s rarely black and white:
- Pre-commercialization
- Obtaining your first customers
- Scaling and expansion
Let’s take a closer look at each stage.
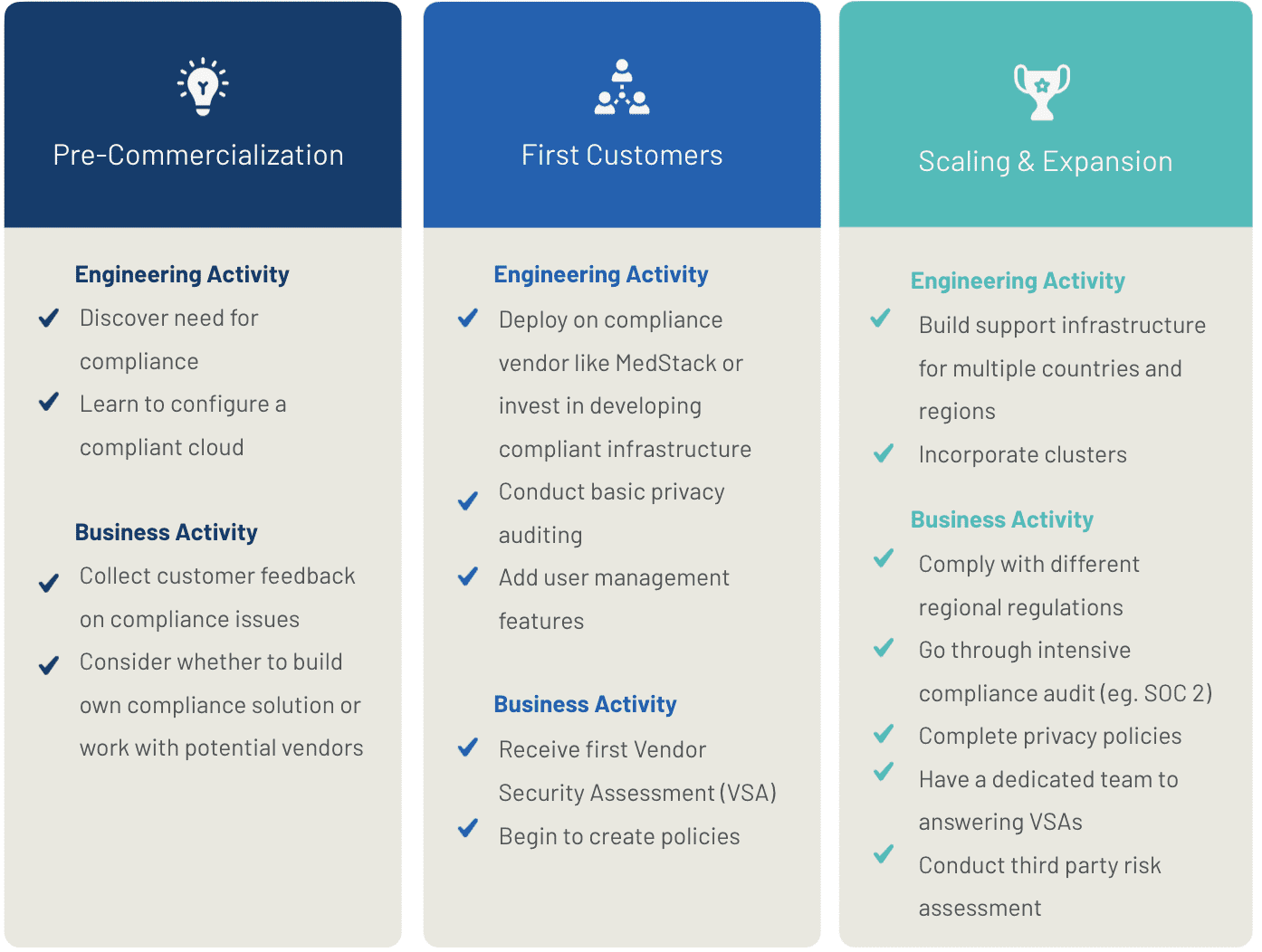
1. Pre-Commercialization
You’re seeking early adopters of your product and testing your assumptions. You might be rolling out a beta amongst a small group of friends and family, or running a pilot with a clinic or a hospital.
If you’re committed to building a strong compliance foundation, consider taking a proactive approach to help avoid serious disruptions down the road.
Start by familiarizing yourself with the basics of HIPAA and the privacy regulations that apply to the region(s) where you do business (eg. the Personal Information Protection and Electronic Documents Act (PIPEDA) in Canada).
Training your employees is also vital to ensuring that any personal health information they may encounter is appropriately safeguarded.
Next, you’ll want to ensure that your application infrastructure is configured in a compliant manner.
At MedStack, we abide by the principle of “compliance by design”. Privacy and security requirements are hard-coded directly into our platform and cover the majority of HIPAA controls out-of-the-box.
You’ll also want to start looking into developing a baseline set of information security policies for your company.
You can choose to develop these from scratch or work with a compliance partner who can provide these for you. MedStack offers the most robust set of inheritable policies on the market and ensures your policies are always up-to-date.
2. Obtaining Your First Customers
So you’ve built a compliant application and you’re ready to start selling. Now it’s time to prove it.
You will likely receive your first Vendor Security Assessment (VSA) at this stage. A VSA is a security questionnaire given to you by a potential customer to satisfy them on your security position.
VSAs differ from customer to customer and most will ask questions in slightly different ways. Here is one example:
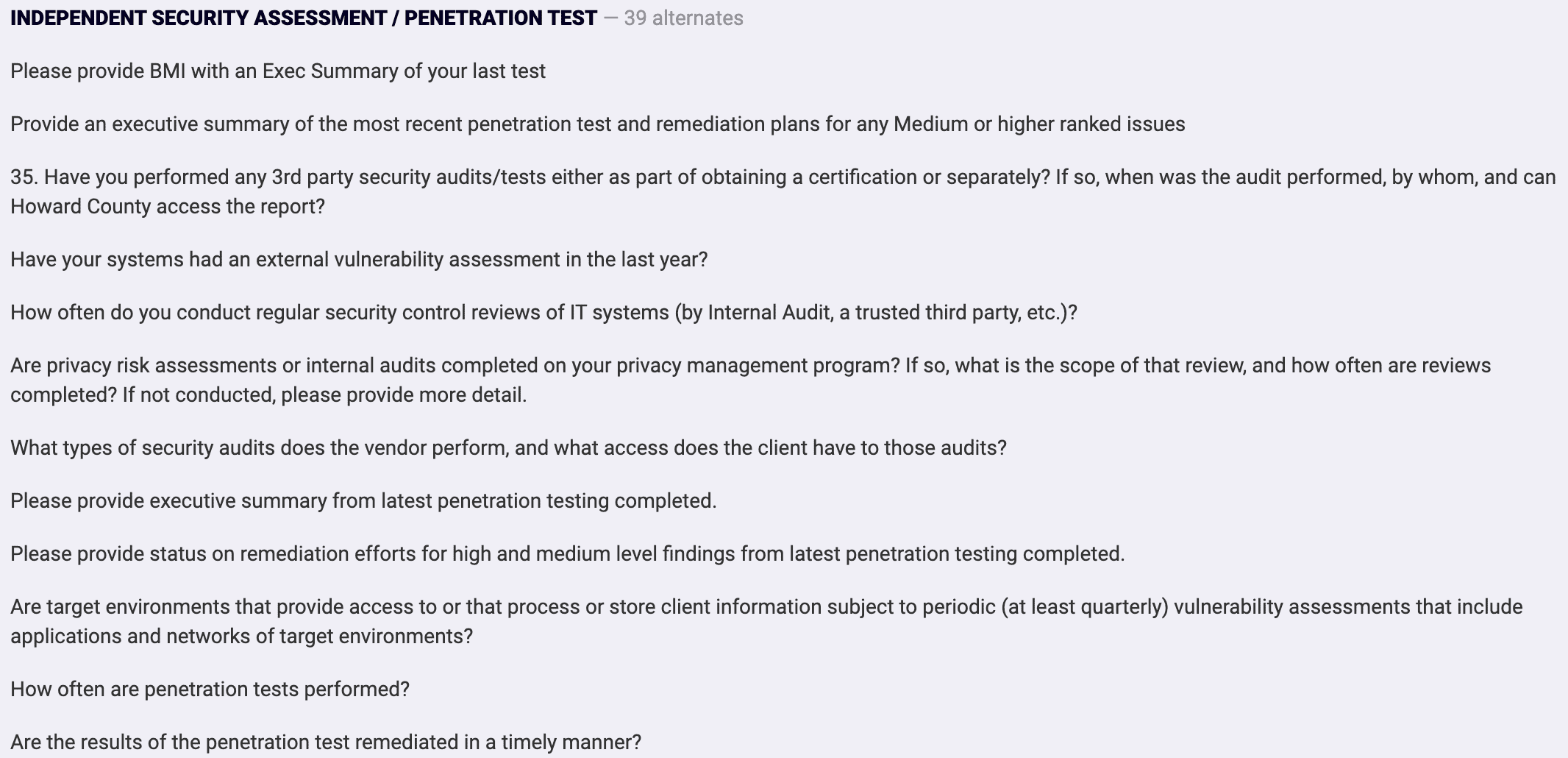
VSAs can be time and resource intensive, but are a necessary part of selling and scaling.
MedStack makes this process faster and easier: simply send them to us and let us answer for you. With hundreds of completed assessments to date, our AI-powered proprietary answer library can answer up to 90% of compliance related questions in less than 7 days.
Your company will also want to adopt agile development methodologies to accelerate the development of your application.
Continuous integration (CI) and continuous delivery (CD) make it easier for your software team to identify defects and quality issues on smaller code differentials rather than larger ones developed over a period of time.
MedStack’s platform has several built-in features to help support these efforts, including with built-in tracking of user events, multi-regional support, a development API for rapid deployment, and monitoring for scale.
3. Scaling and Expansion
Congratulations! Your company is rapidly and consistently growing and you might be looking at international expansion.
It’s important to understand that compliance frameworks vary from region to region. For example, any company looking to do business in Europe, or have customers who are European citizens, is legally required to comply with the European Union’s General Data Protection Regulation (GDPR).
At this stage, your organization will likely also begin pursuing third-party security audits and certifications.
SOC 2 is widely considered the benchmark for trust in the cloud industry, and sends a strong signal to larger organizations that they can have confidence in your security and privacy compliance practices.
A SOC 2 audit can take up to 6 months to complete even with a team fully dedicated to it. MedStack simplifies this process with inheritable SOC 2 controls, making it easier for our customers to obtain their own SOC 2 audits.
Finally, now that your organization’s compliance needs are complex and need to be maintained, it might be in your best interest to hire a dedicated, in-house compliance expert to manage your obligations alongside any third-party partners.
Whether your company is starting out along its journey, or already has some compliance practices in place, MedStack is here to help you succeed. If you’re interested in discussing your own compliance journey, we’d love to talk!